Azure Virtual Network frequently asked questions (FAQ)
06/26/202029 minutes to readAn Azure Virtual Network (VNet) is a representation of your own network in the cloud. It is a logical isolation of the Azure cloud dedicated to your subscription. You can use VNets to provision and manage virtual private networks (VPNs) in Azure and, optionally, link the VNets with other VNets in Azure, or with your on-premises IT infrastructure to create hybrid or cross-premises solutions. Each VNet you create has its own CIDR block and can be linked to other VNets and on-premises networks as long as the CIDR blocks do not overlap. You also have control of DNS server settings for VNets, and segmentation of the VNet into subnets.
Use VNets to:
Create a dedicated private cloud-only VNet. Sometimes you don't require a cross-premises configuration for your solution. When you create a VNet, your services and VMs within your VNet can communicate directly and securely with each other in the cloud. You can still configure endpoint connections for the VMs and services that require Internet communication, as part of your solution.
Securely extend your data center. With VNets, you can build traditional site-to-site (S2S) VPNs to securely scale your datacenter capacity. S2S VPNs use IPSEC to provide a secure connection between your corporate VPN gateway and Azure.
Enable hybrid cloud scenarios. VNets give you the flexibility to support a range of hybrid cloud scenarios. You can securely connect cloud-based applications to any type of on-premises system such as mainframes and Unix systems.
Visit the Virtual network documentation to get started. This content provides overview and deployment information for all of the VNet features.
Yes. You can use a VNet without connecting it to your premises. For example, you could run Microsoft Windows Server Active Directory domain controllers and SharePoint farms solely in an Azure VNet.
Yes. You can deploy a WAN optimization network virtual appliance from several vendors through the Azure Marketplace.
You can use the following tools to create or configure a VNet:
We recommend that you use the address ranges enumerated in RFC 1918, which have been set aside by the IETF for private, non-routable address spaces:
10.0.0.0 - 10.255.255.255(10/8 prefix)172.16.0.0 - 172.31.255.255(172.16/12 prefix)192.168.0.0 - 192.168.255.255 (192.168/16 prefix)Other address spaces may work but may have undesirable side effects.
In addition, you cannot add the following address ranges:
224.0.0.0/4 (Multicast)255.255.255.255/32 (Broadcast)127.0.0.0/8 (Loopback)169.254.0.0/16 (Link-local)168.63.129.16/32 (Internal DNS)Yes. For more information about public IP address ranges, see Create a virtual network. Public IP addresses are not directly accessible from the internet.
Yes. See Azure limits for details. Subnet address spaces cannot overlap one another.
Yes. Azure reserves 5 IP addresses within each subnet. These are x.x.x.0-x.x.x.3 and the last address of the subnet. x.x.x.1-x.x.x.3 is reserved in each subnet for Azure services.
x.x.x.0: Network addressx.x.x.1: Reserved by Azure for the default gatewayx.x.x.2, x.x.x.3: Reserved by Azure to map the Azure DNS IPs to the VNet spacex.x.x.255: Network broadcast address for subnets of size /25 and larger. This will be a different address in smaller subnets.The smallest supported IPv4 subnet is /29, and the largest is /2 (using CIDR subnet definitions).IPv6 subnets must be exactly /64 in size.
No. VNets are Layer-3 overlays. Azure does not support any Layer-2 semantics.
Yes. You can create a route table and associate it to a subnet. For more information about routing in Azure, see Routing overview.
No. Multicast and broadcast are not supported.
You can use TCP, UDP, and ICMP TCP/IP protocols within VNets. Unicast is supported within VNets, with the exception of Dynamic Host Configuration Protocol (DHCP) via Unicast (source port UDP/68 / destination port UDP/67) and UDP source port 65330 which is reserved for the host. Multicast, broadcast, IP-in-IP encapsulated packets, and Generic Routing Encapsulation (GRE) packets are blocked within VNets.
No.
No.
Yes. Subnets can be added to VNets at any time as long as the subnet address range is not part of another subnet and there is available space left in the virtual network's address range.
Yes. You can add, remove, expand, or shrink a subnet if there are no VMs or services deployed within it.
Yes. You can add, remove, and modify the CIDR blocks used by a VNet.
Yes. All services deployed within a VNet can connect outbound to the internet. To learn more about outbound internet connections in Azure, see Outbound connections. If you want to connect inbound to a resource deployed through Resource Manager, the resource must have a public IP address assigned to it. To learn more about public IP addresses, see Public IP addresses. Every Azure Cloud Service deployed in Azure has a publicly addressable VIP assigned to it. You define input endpoints for PaaS roles and endpoints for virtual machines to enable these services to accept connections from the internet.
Yes, VNets can be IPv4-only or dual stack (IPv4+IPv6).For details, see Overview of IPv6 for Azure Virtual Networks.
No. A VNet is limited to a single region. A virtual network does, however, span availability zones. To learn more about availability zones, see Availability zones overview. You can connect virtual networks in different regions with virtual network peering. For details, see Virtual network peering overview
Yes. You can connect one VNet to another VNet using either:
Use the decision table on the Name Resolution for VMs and Role Instances page to guide you through all the DNS options available.
Yes. You can specify DNS server IP addresses in the VNet settings. The setting is applied as the default DNS server(s) for all VMs in the VNet.
Reference Azure limits.
Yes. You can change the DNS server list for your VNet at any time. If you change your DNS server list, you need to perform a DHCP lease renewal on all affected VMs in the VNet, for the new DNS settings to take effect. For VMs running Windows OS you can do this by typing ipconfig /renew directly on the VM. For other OS types, refer to the DHCP lease renewal documentation for the specific OS type.
Azure-provided DNS is a multi-tenant DNS service offered by Microsoft. Azure registers all of your VMs and cloud service role instances in this service. This service provides name resolution by hostname for VMs and role instances contained within the same cloud service, and by FQDN for VMs and role instances in the same VNet. To learn more about DNS, see Name Resolution for VMs and Cloud Services role instances.
There is a limitation to the first 100 cloud services in a VNet for cross-tenant name resolution using Azure-provided DNS. If you are using your own DNS server, this limitation does not apply.
Yes. You can set DNS servers per VM or cloud service to override the default network settings. However, it's recommended that you use network-wide DNS as much as possible.
No. You cannot specify a custom DNS suffix for your VNets.
Yes. All network interfaces (NIC) attached to a VM deployed through the Resource Manager deployment model must be connected to a VNet. VMs deployed through the classic deployment model can optionally be connected to a VNet.
Private: Assigned to each NIC within each VM. The address is assigned using either the static or dynamic method. Private IP addresses are assigned from the range that you specified in the subnet settings of your VNet. Resources deployed through the classic deployment model are assigned private IP addresses, even if they're not connected to a VNet. The behavior of the allocation method is different depending on whether a resource was deployed with the Resource Manager or classic deployment model:
Resource Manager: A private IP address assigned with the dynamic or static method remains assigned to a virtual machine (Resource Manager) until the resource is deleted. The difference is that you select the address to assign when using static, and Azure chooses when using dynamic.Classic: A private IP address assigned with the dynamic method may change when a virtual machine (classic) VM is restarted after having been in the stopped (deallocated) state. If you need to ensure that the private IP address for a resource deployed through the classic deployment model never changes, assign a private IP address with the static method.Public: Optionally assigned to NICs attached to VMs deployed through the Azure Resource Manager deployment model. The address can be assigned with the static or dynamic allocation method. All VMs and Cloud Services role instances deployed through the classic deployment model exist within a cloud service, which is assigned a dynamic, public virtual IP (VIP) address. A public static IP address, called a Reserved IP address, can optionally be assigned as a VIP. You can assign public IP addresses to individual VMs or Cloud Services role instances deployed through the classic deployment model. These addresses are called Instance level public IP (ILPIP addresses and can be assigned dynamically.
No. You cannot reserve a private IP address. If a private IP address is available, it is assigned to a VM or role instance by the DHCP server. The VM may or may not be the one that you want the private IP address assigned to. You can, however, change the private IP address of an already created VM, to any available private IP address.
It depends. If the VM was deployed through Resource Manager, no, regardless of whether the IP address was assigned with the static or dynamic allocation method. If the VM was deployed through the classic deployment model, dynamic IP addresses can change when a VM is started after having been in the stopped (deallocated) state. The address is released from a VM deployed through either deployment model when the VM is deleted.
Yes, but it's not recommended unless necessary, such as when assigning multiple IP addresses to a virtual machine. For details, see Adding multiple IP addresses to a virtual machine. If the IP address assigned to an Azure NIC attached to a VM changes, and the IP address within the VM operating system is different, you lose connectivity to the VM.
Nothing. The IP addresses (public VIP, public, and private) remain assigned to the cloud service deployment slot or VM.
Yes. You can find more information in the How to move a VM or role instance to a different subnet article.
No. A MAC address cannot be statically configured.
Yes, the MAC address remains the same for a VM deployed through both the Resource Manager and classic deployment models until it's deleted. Previously, the MAC address was released if the VM was stopped (deallocated), but now the MAC address is retained even when the VM is in the deallocated state. The MAC address remains assigned to the network interface until the network interface is deleted or the private IP address assigned to the primary IP configuration of the primary network interface is changed.
Yes. All VMs and Cloud Services role instances deployed within a VNet can connect to the Internet.
Yes. You can deploy Web Apps inside a VNet using an ASE (App Service Environment), connect the backend of your apps to your VNets with VNet Integration, and lock down inbound traffic to your app with service endpoints. For more information, see the following articles:
Yes. You can (optionally) deploy Cloud Services role instances within VNets. To do so, you specify the VNet name and the role/subnet mappings in the network configuration section of your service configuration. You do not need to update any of your binaries.
Yes. You must connect a virtual machine scale set to a VNet.
Yes, For details, see Virtual network integration for Azure services.
Resources deployed through some Azure PaaS services (such as Azure Storage and Azure SQL Database), can restrict network access to VNet through the use of virtual network service endpoints or Azure Private Link. For details, see Virtual network service endpoints overview, Azure Private Link overview
No. You cannot move services in and out of VNets. To move a resource to another VNet, you have to delete and redeploy the resource.
VNets are isolated from one another, and other services hosted in the Azure infrastructure. A VNet is a trust boundary.
Yes. You can apply Network Security Groups to individual subnets within a VNet, NICs attached to a VNet, or both.
Yes. You can deploy a firewall network virtual appliance from several vendors through the Azure Marketplace.
Yes. For details, see Azure Network Security Overview.
No. Virtual Networks doesn't store any customer data.
Yes. You can use REST APIs for VNets in the Azure Resource Manager and classic deployment models.
Yes. Learn more about using:
VNet peering (or virtual network peering) enables you to connect virtual networks. A VNet peering connection between virtual networks enables you to route traffic between them privately through IPv4 addresses. Virtual machines in the peered VNets can communicate with each other as if they are within the same network. These virtual networks can be in the same region or in different regions (also known as Global VNet Peering). VNet peering connections can also be created across Azure subscriptions.
Yes. Global VNet peering enables you to peer VNets in different regions. Global VNet peering is available in all Azure public regions, China cloud regions, and Government cloud regions. You cannot globally peer from Azure public regions to national cloud regions.
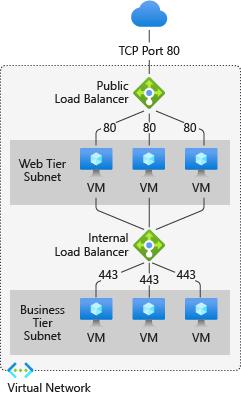
If the two virtual networks in two different regions are peered over Global VNet Peering, you cannot connect to resources that are behind a Basic Load Balancer through the Front End IP of the Load Balancer. This restriction does not exist for a Standard Load Balancer.The following resources can use Basic Load Balancers which means you cannot reach them through the Load Balancer's Front End IP over Global VNet Peering. You can however use Global VNet peering to reach the resources directly through their private VNet IPs, if permitted.
VMs behind Basic Load BalancersVirtual machine scale sets with Basic Load BalancersRedis CacheApplication Gateway (v1) SKUService FabricAPI Management (stv1)Active Directory Domain Service (ADDS)Logic AppsHDInsightAzure BatchApp Service EnvironmentYou can connect to these resources via ExpressRoute or VNet-to-VNet through VNet Gateways.
Yes. It is possible to establish VNet Peering (whether local or global) if your subscriptions belong to different Azure Active Directory tenants. You can do this via Portal, PowerShell or CLI.
If your peering connection is in an Initiated state, this means you have created only one link. A bidirectional link must be created in order to establish a successful connection. For example, to peer VNet A to VNet B, a link must be created from VNetA to VNetB and from VNetB to VNetA. Creating both links will change the state to Connected.
If your VNet peering connection is in a Disconnected state, it means one of the links created was deleted. In order to re-establish a peering connection, you will need to delete the link and recreate it.
Yes. You can peer VNets across subscriptions and across regions.
No. Address spaces must not overlap to enable VNet Peering.
No. You can only enable the 'Use Remote Gateway' option on one peering to one of the VNets.
There is no charge for creating a VNet peering connection. Data transfer across peering connections is charged. See here.
When Azure traffic moves between datacenters (outside physical boundaries not controlled by Microsoft or on behalf of Microsoft), MACsec data-link layer encryption is utilized on the underlying network hardware.This is applicable to VNet peering traffic.
VNet peering connections go into Disconnected state when one VNet peering link is deleted. You must delete both links in order to reestablish a successful peering connection.
No. Transitive peering is not supported. You must peer VNetA and VNetC for this to take place.
No. VNet peering, whether local or global, does not impose any bandwidth restrictions. Bandwidth is only limited by the VM or the compute resource.
Here is a troubleshooter guide you can try.
Virtual network TAP preview is available in all Azure regions. The monitored network interfaces, the virtual network TAP resource, and the collector or analytics solution must be deployed in the same region.
Filtering capabilities are not supported with the virtual network TAP preview. When a TAP configuration is added to a network interface a deep copy of all the ingress and egress traffic on the network interface is streamed to the TAP destination.
A monitored network interface can have only one TAP configuration. Check with the individual partner solution for the capability to stream multiple copies of the TAP traffic to the analytics tools of your choice.
Yes. The same virtual network TAP resource can be used to aggregate mirrored traffic from monitored network interfaces in peered virtual networks in the same subscription or a different subscription. The virtual network TAP resource and the destination load balancer or destination network interface must be in the same subscription. All subscriptions must be under the same Azure Active Directory tenant.
Virtual network TAP is in preview. During preview, there is no service level agreement. The capability should not be used for production workloads. When a virtual machine network interface is enabled with a TAP configuration, the same resources on the Azure host allocated to the virtual machine to send the production traffic is used to perform the mirroring function and send the mirrored packets. Select the correct Linux or Windows virtual machine size to ensure that sufficient resources are available for the virtual machine to send the production traffic and the mirrored traffic.
You will be able to add a TAP configuration on a network interface attached to a virtual machine that is enabled with accelerated networking. But the performance and latency on the virtual machine will be affected by adding TAP configuration since the offload for mirroring traffic is currently not supported by Azure accelerated networking.
There are two steps to secure an Azure service resource through service endpoints:
Turn on service endpoints for the Azure service.Set up VNet ACLs on the Azure service.The first step is a network side operation and the second step is a service resource side operation. Both steps can be performed either by the same administrator or different administrators based on the Azure RBAC permissions granted to the administrator role. We recommend that you first turn on service endpoints for your virtual network prior to setting up VNet ACLs on Azure service side. Hence, the steps must be performed in the sequence listed above to set up VNet service endpoints.
Note
Both the operations described above must be completed before you can limit the Azure service access to the allowed VNet and subnet. Only turning on service endpoints for the Azure service on the network side does not provide you the limited access. In addition, you must also set up VNet ACLs on the Azure service side.
Certain services (such as SQL and CosmosDB) allow exceptions to the above sequence through the IgnoreMissingVnetServiceEndpoint flag. Once the flag is set to True, VNet ACLs can be set on the Azure service side prior to setting up the service endpoints on the network side. Azure services provide this flag to help customers in cases where the specific IP firewalls are configured on Azure services and turning on the service endpoints on the network side can lead to a connectivity drop since the source IP changes from a public IPv4 address to a private address. Setting up VNet ACLs on the Azure service side before setting service endpoints on the network side can help avoid a connectivity drop.
No, not all Azure services reside in the customer's virtual network. The majority of Azure data services such as Azure Storage, Azure SQL, and Azure Cosmos DB, are multi-tenant services that can be accessed over public IP addresses. You can learn more about virtual network integration for Azure services here.
When you use the VNet service endpoints feature (turning on VNet service endpoint on the network side and setting up appropriate VNet ACLs on the Azure service side), access to an Azure service is restricted from an allowed VNet and subnet.
The VNet service endpoint feature (turning on VNet service endpoint on the network side and setting up appropriate VNet ACLs on the Azure service side) limits the Azure service access to the allowed VNet and subnet, thus providing a network level security and isolation of the Azure service traffic. All traffic using VNet service endpoints flows over Microsoft backbone, thus providing another layer of isolation from the public internet. Moreover, customers can choose to fully remove public Internet access to the Azure service resources and allow traffic only from their virtual network through a combination of IP firewall and VNet ACLs, thus protecting the Azure service resources from unauthorized access.
VNet service endpoints help protect Azure service resources. VNet resources are protected through Network Security Groups (NSGs).
No, there is no additional cost for using VNet service endpoints.
Yes, it is possible. Virtual networks and Azure service resources can be either in the same or different subscriptions. The only requirement is that both the virtual network and Azure service resources must be under the same Active Directory (AD) tenant.
Yes, it is possible when using service endpoints for Azure Storage and Azure Key Vault. For rest of services, VNet service endpoints and VNet ACLs are not supported across AD tenants.
By default, Azure service resources secured to virtual networks are not reachable from on-premises networks. If you want to allow traffic from on-premises, you must also allow public (typically, NAT) IP addresses from your on-premises or ExpressRoute. These IP addresses can be added through the IP firewall configuration for the Azure service resources.
To secure Azure services to multiple subnets within a virtual network or across multiple virtual networks, enable service endpoints on the network side on each of the subnets independently and then secure Azure service resources to all of the subnets by setting up appropriate VNet ACLs on the Azure service side.
If you want to inspect or filter the traffic destined to an Azure service from a virtual network, you can deploy a network virtual appliance within the virtual network. You can then apply service endpoints to the subnet where the network virtual appliance is deployed and secure Azure service resources only to this subnet through VNet ACLs. This scenario might also be helpful if you wish to restrict Azure service access from your virtual network only to specific Azure resources using network virtual appliance filtering. For more information, see egress with network virtual appliances.
The HTTP 403 or HTTP 404 error is returned.
Yes, for most of the Azure services, virtual networks created in different regions can access Azure services in another region through the VNet service endpoints. For example, if an Azure Cosmos DB account is in West US or East US and virtual networks are in multiple regions, the virtual network can access Azure Cosmos DB. Storage and SQL are exceptions and are regional in nature and both the virtual network and the Azure service need to be in the same region.
Yes, a VNet ACL and an IP firewall can co-exist. Both features complement each other to ensure isolation and security.
Deletion of VNets and subnets are independent operations and are supported even when service endpoints are turned on for Azure services. In cases where the Azure services have VNet ACLs set up, for those VNets and subnets, the VNet ACL information associated with that Azure service is disabled when a VNet or subnet that has VNet service endpoint turned on is deleted.
The deletion of an Azure service account is an independent operation and is supported even when the service endpoint is enabled on the network side and VNet ACLs are set up on Azure service side.
When virtual network service endpoints are enabled, the source IP addresses of the resources in your virtual network's subnet switches from using public IPV4 addresses to the Azure virtual network's private IP addresses for traffic to Azure service. Note that this can cause specific IP firewalls that are set to public IPV4 address earlier on the Azure services to fail.
Service endpoints add a system route which takes precedence over BGP routes and provides optimum routing for the service endpoint traffic. Service endpoints always take service traffic directly from your virtual network to the service on the Microsoft Azure backbone network. For more information about how Azure selects a route, see Azure Virtual network traffic routing.
No, ICMP traffic that is sourced from a subnet with service endpoints enabled will not take the service tunnel path to the desired endpoint. Service endpoints will only handle TCP traffic. This means that if you want to test latency or connectivity to an endpoint via service endpoints, tools like ping and tracert will not show the true path that the resources within the subnet will take.
To reach the Azure service, NSGs need to allow outbound connectivity. If your NSGs are opened to all Internet outbound traffic, then the service endpoint traffic should work. You can also limit the outbound traffic to service IPs only using the Service tags.
Service endpoints can be configured on a virtual network independently by a user with write access to the virtual network. To secure Azure service resources to a VNet, the user must have permission Microsoft.Network/virtualNetworks/subnets/joinViaServiceEndpoint/action for the subnets being added. This permission is included in the built-in service administrator role by default and can be modified by creating custom roles. Learn more about built-in roles and assigning specific permissions to custom roles.
Virtual network (VNet) service endpoint policies allow you to filter virtual network traffic to Azure services, allowing only specific Azure service resources over the service endpoints. Endpoint policies provide granular access control from the virtual network traffic to the Azure services. You can learn more about the service endpoint policies here.
Azure Active Directory (Azure AD) doesn't support service endpoints natively. Complete list of Azure Services supporting VNet service endpoints can be seen here. Note that the "Microsoft.AzureActiveDirectory" tag listed under services supporting service endpoints is used for supporting service endpoints to ADLS Gen 1. For ADLS Gen 1, virtual network integration for Azure Data Lake Storage Gen1 makes use of the virtual network service endpoint security between your virtual network and Azure Active Directory (Azure AD) to generate additional security claims in the access token. These claims are then used to authenticate your virtual network to your Data Lake Storage Gen1 account and allow access. Learn more about Azure Data Lake Store Gen 1 VNet Integration
There is no limit on the total number of VNet service endpoints in a virtual network. For an Azure service resource (such as an Azure Storage account), services may enforce limits on the number of subnets used for securing the resource. The following table shows some example limits:
Azure serviceLimits on VNet rulesAzure Storage100Azure SQL128Azure Synapse Analytics128Azure KeyVault200Azure Cosmos DB64Azure Event Hub128Azure Service Bus128Azure Data Lake Store V1100Note
The limits are subjected to changes at the discretion of the Azure service. Refer to the respective service documentation for services details.
PREV: Creating a first Windows Server 2012 Domain Controller ...
NEXT: Understanding Active Directory in Windows Server 2012 R2 ...